IF THE PROCESSOR AFFECT MELTDOWN OR SPECTRE
Meldown and Specter vulnerabilities affect ALL processors in the world, regardless of the operating system.
In recent days, the international press has begun to speculate on the subject of the Meltdown and Specter vulnerabilities discovered in the Intel AMD and ARM processors.
The right option!
The truth is that intel has a serious vulnerability on all processors manufactured in the LAST 10 YEARS…. LAST 10 YEARS ????
These days the information comes to the surface; why? Because it was too hard a blow and hard to bear, and they probably waited to find something at AMD or ARM, as… shares the damage with them. It's not a personal matter, it's just propaganda and marketing.
How Affected Are the Processors?
INTEL is the most affected by this situation because it has the worst vulnerability that is impossible to repair because it is hardware.
What is hardware vulnerability?
It seems that Intel intentionally left some loopholes open in their processors, and even "ambushes installed in the processor".
Intel has installed operating systems in the processor?
Believe it or not, intel is installed in a remote operating system that can read data stored on disks.
The operating system is very small, just the kernel and a few modules. This operating system installed by the Intel processors is called MINIX. Madărfacării .... !!!
How do you know if you have Meltdown or Specter?
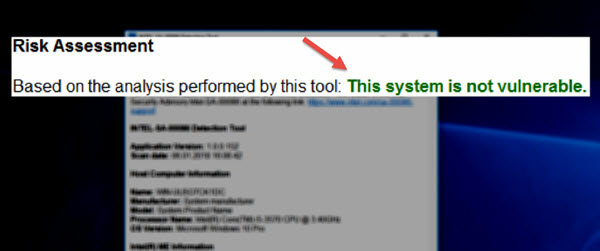
You can find a small software on the Intel website to detect the presence of danger. link below
How to repair the vulnerable processor affected by Meltdown and Specter?
Microsoft released an update that solves the problem. If you do not have the updates turned on, you have a direct download link below.
Linux and macOS will also release updates if they have already done so.
Download:
Meltdown and Specter vulnerability detection "tool"
The update that "fixes" the Meltdown and Specter vulnerability (if you do not have open updates)
-
Related Tutorials:
- Infection live with WANNA CRY Ransomware and methods of protection
- Anti ransomware anti-encryption NEW files in Windows Defender
- Maximum security with Wi-Fi aka Radius server. WPA Enterprise




You're special!
The update that "resolves" Meltdown and Specter vulnerability and win8?
Well, that's it, with the quotes. I said in the tutorial that the problem on Intel processors is hardware, and this update is that some kind of PLASTURE is not a repair.
HAPPY BIRTHDAY !
I would like to talk about a collaboration in Canada…
I did this update but tells me the computer is still vulnerable. What can I do?
I knew why I've been on AMD for almost 15 years !!! 🙂 Many of us don't even realize how serious the problem is! Of course, a normal user does not have to worry but I am thinking of large and multinational companies, governments and security agencies, etc.…
ALL CPUs are affected. Intel's Intel processors are the most affected, but AMD or ARM is affected as well.
I have two intel due you know what the intel told me that such processors do not get support from them! If not from them then from who ?????
Here's how it says to me: This system is vulnerable, even today I received this update: 2018-01 Monthly Security Update Updates for Windows 7 for x64 based systems (KB4056894) The test I made after this update, I hope that it is seen as using windows 7.
I have the update and it still seems to be vulnerable, intel g4400
I said that information and I use windows xNUMX enterprise x10 with unpinned update
I give error when I want to update and I have my pc vulnerable
I have not received any updates like this ..
It will not shake in vain. The stuff here is and will always be, the problem for us is not this, because it has not been reported anything related to leaked information related or related to this problem. And if there is something important NSA questions, if that is the case, or hackers will not steal your pictures with sausages when you smoke them. IMPORTANT is how to keep away the programs that make the slave processors for the bitcoin mining. 50 beta work that he does something like that.
I did not update. Message: Based on the analysis performed by this tool: This system is not vulnerable. PS Intel i7-3537U CPU @ 2.00GHz
I did the update, I restarted the pc and… This system is vulnerable. So it doesn't work.
An update from Intel will come soon. I keep you up to date.
Mr. Cristi A video tutorial on IPTV can be used abroad on smart TV too, I have seen that what's on telekom have this internet television service. Thank you
I received the update via windows update KB4056892 I did the test and it seems to me that it is not vulnerable. Now, after updating to me, there was a problem with AI Suite II from the ASUS motherboard which is not working for me anymore (Al Suite II is no longer working).
Perhaps AI Suite used this backdoor (vulnerability) to access certain data.
hello to me, I have windows 8.1 with Asus motherboard and the same AI Suite II gives me a bug. after this update KB4056895, now I uninstalled the update and went dreaqu, that I gave a lot of money on the processor with the motherboard to have the performance, and now they want to do the same strategy as the iphone, it decreases the frequency to the latter to go harder, more Romanian to drop them out of performance and sell their new smartphones. not ordinary orgasms ..
I also had backup to the system I did and I checked without this update if it is vulnerable. After checking, she writes that the system is not vulnerable and I have Intel i5 processor and Windows 10 pro 64 bit.
DO NOT put a stop to these tampons. It is part of the "country wants you bad" cycle to make it easier for you. The biggest enemy of manipulators is the processor. I'm surprised that Cristi is "seduced" so easily. But you know!
This with: "The country wants you badly", is true, and always has been.
Computers can also be instruments that we are manipulating, but also tools that can awaken us. It depends on everyone wanting to use their PC, laptops, phone, etc.
Still I did not understand how the manipulator's enemy is the processor?
So after I recovered my system backup I tested if it was vulnerable and without that update and the result was that it was not vulnerable and Al Suite worked smoothly after the update I did not work anymore. I do not know why. So, with Al Suite, the system was not vulnerable when I checked, and as I said I have the i5 Ivy Bridge processor and windows 10 pro 64 bit. I do not have cracky programs including windows is activated without crack or other wonders. That does not understand what happened to Al Suite no longer works after that update.
@Cristian Cismaru
"Still, I didn't understand how the enemy of manipulators is the processor?"
Well let me explain how:
All listed above (phone, tablet, laptop, PC) each have a processor.
Recently in Iran, Instagram, Twiter, was banned.
China has been banned from facebook.
In Russia it was banned…
They all use processors!
Lately, there are some news on our televisions that parents should close their monitors, tablets, and their children's phones.
All of this has processors.
Would you like your girl not to have the phone at school?
If you do not understand this time, you do not want to.
About blocking social networks.
In some countries, certain social networks are banned, not the entire internet; this is because networks that Facebook and Twitter are used to handle the population. I know it sounds weird, but that's the way it is.
The Arab Spring was more a spring that brought regime changes that the powers of the world longed for.
The people of those countries have been swept away and now it is a humanitarian, cultural, environmental and economic disaster.
About Syria and Yemen I do not even speak.
As neither was a revolution in us, neither in the Arab countries was a spontaneous move.
Nothing is accidental.
About the news that appears on TV.
Everything appearing on television is designed to shape public perception.
This propaganda makes people stand in a state of fear, and televisions are perceived as the source of truth, a true friend of the public.
Apart from propaganda, the televisions will also have a market share that they can not win if the world stays too much on the net.
About baby phones.
My girl does not have a phone connected to the net and no social accounts.
In schools there should be a rule regarding the use of telephones, because the telephone in the end is a "fun", which disturbs our attention. I say that at least at school children should be careful, if we want a beautiful future.
About Social Networks.
Though regarded as a heavenly hand of the century, these are the most toxic things in our lives.
Social networks change our behavior, relationships between us, the level of patience.
Try to stay at least 48 for hours without social networking. You will feel the psychic withdrawal as you push.
We drop a post on facebook, as if we dropped the water in the pond, waiting for the catch of the likes. We want more and more. We have less and less patience. We sit at the table, two friends, and each one of us is in the phone.
In the direct relationship, people become extremely anxious, they quickly lose their patience, lose their thoughts in a discussion. People do not use longer phrases to express a certain event nicely, but they use short phrases and say in a rush, as if they are looking for a liking.
The processor is only an instrument that can be used constructively for other purposes. You can use a knife to cut vegetables for a recipe, carve something nice, or kill someone.
The processor (the computer) is the reflection of our needs and desires in the virtual environment.
These vulnerabilities show that the processor was also a Trojan horse.
There is also the Intel vs AMD vs. ARM discussion. Few people know that these very important companies and others have the same shareholders.
Conclusion.
As can be seen, these processors, like any other "tool", come with two blades from the factory. It's up to you to be entertained or just get what you need.
Consume the information, do not waste your information.
There would be a lot to say
Correct comment that reflects reality. Subscribe.
My I5 4460 is not vulnerable. I do not understand why some are and others are not vulnerable being produced by the same company.
Stay quiet, as 10 has never felt any vulnerability. There are others you do not feel. It's like an 3,2 earthquake on Richter
Hello! After scanning with this utility the result is this: Detection Error: This system may be vulnerable either the intel (R) MEI / TXEI driver is not installed (available from your system manufacturer) or the system manufacturer does not allow access to the ME / TXE from the host driver.
I find it unclear to describe this vulnerability and patch.
Since it is indeed a hardware vulnerability, the patch is software-like, so this patch does not fix, bandwidth, but simply disables that hardware component of the processor that is affected by that vulnerability.
In other words, you will have a processor that does not work on the initial parameters after this update, even the operating system makers, Microsoft, Red Hat have removed these patches, but statistics show that about 20% of CPU performance will be lost applying that patch.
So, for regular users, gamers, and others who have paid some bundles on these processors, is it normal to have this performance drop after they've given that money? My opinion is that there should be more lobbies here, not elsewhere.
Intel® Core ™ i3-7100U vulnerable after update? What is the solution?
to give yourself the head of the walls :) to be, as long as you are not a president, a minister, an important person, not one who smoked sausages behind the block of fear not to come guard, has nothing to be afraid. Repeat will not come and no one will come to you for the sake of entering, unless you were someone in the living alley.
This is the complex of inferiority. We have the impression that we are not so important.
We are very important, and above all, our privacy is important.
You will not think so small and unimportant! A president is nothing more than us, but on the contrary, he should be our servant.
And let me not hear that nonsense with: "I have nothing to hide" or "If you are honest, you have nothing to fear"; this is manipulation meant to discourage our self-defense, it is called "poisoning the well".
Be Careful.
Freedom and intimacy today is not lost at once, but in small steps that are more difficult to feel.
Big Brother Law + Some Orders + a Backdoor in Computer + etc.
Hello, you, Cristi and Adrian, can make a channel like: Zaiafet, Attention mad apple, Top 8
@Cristian Cismaru The best way to get rid of the Intel Management backdoor and MINIX OS implicitly involves using me_cleaner. It's on Github. How to for Windows here: https://www.reddit.com/r/privacy/comments/77ut68/disabling_intel_me/
After application, no Intel processor will be vulnerable, so no more software patching will be needed because the ME chip will be deactivated leaving only the modules needed to enable BIOS initialization and booting the operating system.
Hello! After scanning with this utility the result is this:
Detection Error: This system may be vulnerable either the intel (R) MEI / TXEI driver is not installed or your system manufacturer does not allow access to the ME / TXE from the host driver.
It appears to me like George, where I notice you did not answer.
So, what is the problem with us, does this result appear? Note that the computer has made that KB4056894 update
I am waiting for an answer.
Goods.
Hello.
I have 2017-11 Update for Windows 10 Version 1709 for x64-based Systems (KB4054022) installed and the Intel-SA-00086-GUI utility says the system is vulnerable.
I have the Intel i5-6600K CPU
What is the situation ?
I did not find debugging tool for Windows 7 64 bit. Does anyone have?
No, I had an answer to a fb group on Tuesday or Wednesday to wait for that.
That's how it looks like firmware ME after removing:
[Img] https://i.imgur.com/2KI3vp2.png [/ img]
We will have to change our processors. Maybe that's the intention of processor manufacturers. I think a saturation has been reached and then they threw that away with vulnerability. We have to change our processors, implicitly the motherboards, and that's how a few billion greens will go into their pockets. That with "I have nothing to hide" - I do not agree with her. I want my privacy not to be violated in any way. I paid honestly for the PC, I have non-pirated Windows, so I want them to be fair to me too. If the only way to get rid of this vulnerability (without losing processor performance) is to change our processors, then they should change them for free. I seem to see that the next generation of processors come without this vulnerability….
Right punctuated. It's probably a guerrilla marketing tactic that raises a new form of consumerism.
CONSUMER 2.0
The world was too happy with the old computer of 5 years, that it was doing pretty well. Now, after these vulnerabilities, the same PC seems to be sick, touched by some serious illness; and of course you do not trust him anymore.
The solution… ..a new one… .that spoils the processors on the shelves.
Let me give you an example. Until recently, the upper limit for blood glucose was 180. Pharmaceutical companies in collusion with some doctors who were in public, lowered the upper limit to 110. What happened next? Those who were healthy between 110 and 180, suddenly now were sick and had to buy their medicine. And that's how billions began to flow to drug companies… .. So with these. Most people with PCs are good and a PC from 5 years ago (not about those who need high computing power such as video editing and others) for browsing, movies and lighter stuff. But how to make them change PCs? Especially since they are the majority :)))?
A Big Brother law should definitely be dated, people die in injured parks, children violated in the elevator, thieves in the suburban, people pushed to the subway, children bite in the park and kill the ",,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,, there big brother, there are cameras everywhere, in the elevator, on the street, there if you did something in 5 minutes I find you PRACTICALLY NOT HOW TO SCAPE, stop talking about New York, they are around each other. I keep on my privacy, but above all, it's justice, and when we talk about it means that if you've done something to find yourself in 5 minutes, do not let go of other troubles.
Perception is everything.
Today, the crime rate is no bigger than last year. The only difference is that all the misfortunes across the country are centralized in news and quickly presented one after another. Our mind perceives all this as an imminent danger.
We have the impression that we are caught in a whirlwind where only crimes, rapes, corruption, stupidity, etc. are produced.
The crime rate in Romania is among the lowest in Europe.
Our perception is deformed INTENTIONAL.
https://www.catalog.update.microsoft.com/Search.aspx?q=KB4056892 - I think this is the link to the good update. What is in the text of the tutorial is from November.
Hi, if i have Linux what do I have to do?
I have to mention that I used windows7 until December last year
Update to date, nothing special.
Hi.
I need a software to get out of Chrome when I search on a page
: https://duckduckgo.com/
I tried with the spyhunter and on the extensions I can not find anything.
Thanks in advance!
Duckduckgo.com is not an extension is a web search engine
Simply go into the browser settings and change the search engine!
Not all Intel processors, complete information: https://www.intel.com/content/www/us/en/support/articles/000025619/software.html
And as a demo: http://i66.tinypic.com/iz29eb.png
Hello and respect for everything you do for free.
But, as paul75 said a bit higher, it seems
that there are some other reasons why a system goes turbulent and
pull from networks (current and net), all he can.
It's about crypocurrency malware miners.
monero, moloko, slmgr32, svchost.exe.exe, vshub etc!
I think here's the point to make a profound analysis of the vulnerabilities.
(slowly teaches the world how to put on a scarf when the wind blows'… I say)
https://blogs.opera.com/desktop/2017/12/opera-50-beta-rc-cryptocurrency-mining-protection/ . For cryptomonas, 50 works right in the beta phase, but as rumored it would be the best on the market. With the free avast version of the virus, we found a virus for cryptomonas.
The update has slowed down my Linux, so please set up a system with a Meltdown and Specter free processor
… .I have long since separated myself, the “net part” from the “working part”! At first it was "over my hand"… but I'm glad I wasn't wrong about "personal data security"… ..I use 2 computers and a laptop …… .one of the computers, "didn't see" the network , not even a picosecond… ..and…. ”works” every day (on it I have a xp “bald” of many useless and malicious things) …… .And as a “crazy dream” I would like someone to - sue them for "planting" their shit to spy on us and steal our personal data… .and take a cart of money!